Cybernation of AWS Multi Account Management
Cybernation of AWS Multi Account Management
Many of the AWS customers create separate AWS accounts for each business units to meet the different needs of their organization. Even though creating multiple accounts provides benefits like compliance, security, control access, simplified billing and shared resources, creating and configuring these accounts manually takes a lot of time. To overcome this, in this blog we will give an overview of account creation automation and setting up tasks like creating users with the appropriate privileges, configuring custom networks and maintaining the governance policies.
AWS services discussed in this blog post:
- AWS Organizations offers policy-based management for multiple AWS accounts. Organizations helps centrally manage billing, control access, compliance and security and share resources across the member AWS accounts. It can create groups of accounts, automate account creation, apply and manage policies for those groups.
- AWS Service Catalog allows to create and manage catalogs of services that are approved for use on AWS.
- AWS CloudFormation uses a simple text file to model and provision, in an automated and secure manner, all the resources needed for the applications across all regions and accounts.
- AWS Lambda runs code without provisioning or managing servers. The Charge is based on the compute time consumed. There is no charge when the code is not running.
- AWS Simple Storage Service (S3) is an object storage service.
Terms and Concepts
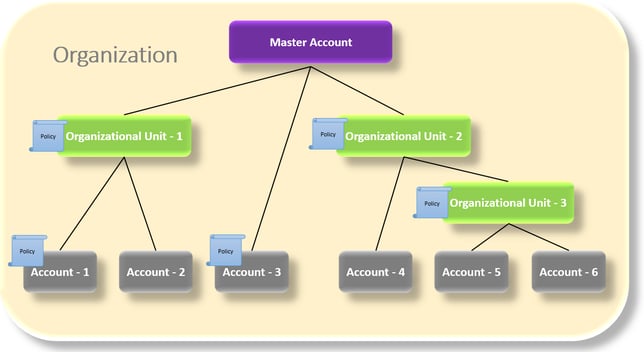
Root: The parent container for all the accounts in an organization.
Organization unit (OU): A container for accounts within a root. An OU also can contain other OUs, enabling a hierarchy that resembles an upside-down tree, with a root at the top and branches of OUs that reach down, ending in accounts that are the leaves of the tree.
Account: A standard AWS account that contains the AWS resources.
Service control policy (SCP): A policy that specifies the services and actions that users and roles can use in the accounts that the SCP affects. SCPs are similar to IAM permission policies.
The following diagram shows a basic organization that consists of six accounts that are organized into three organizational units (OUs) under the master account. The organization also has several policies that are attached to some of the OUs or directly to accounts.
We can able to automate this process in several ways. Here we will discuss about one such automation method.
The following architecture outlines the process flow involved with the Account Creation Automation:
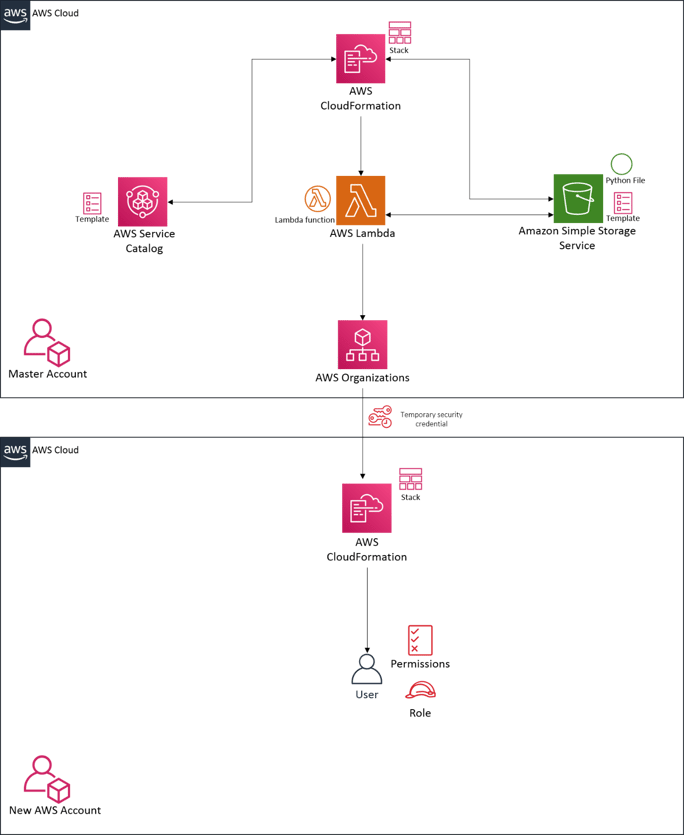
Automation Process Overflow:
- Create an AWS Service Catalog Product in the master account with the template which contains the configuration details of lambda service.
- Launching the Service Catalog Product, a cloud formation stack will be created with the configurations mentioned in the template in the master account.
- On a successful creation of the stack, a lambda function will be created and invoked.
- The lambda function consists of the API calls which is responsible for the below activities
- Create a new member account
- Create an organizational unit (Optional)
- Move the new member account to the organization unit (Optional)
- Create a Service Control Policy with the appropriate privileges.
- Assign the created SCP to the newly Created AWS account
- Assume a role and create temporary credentials to access the newly created account
- Get the template from S3 bucket in the master account to create a Cloud Formation Stack in the newly created account which is then responsible for creating users with the appropriate privileges
- Once the lambda function gets executed successfully, a new member account is created and configured successfully.
- For the new AWS member to login, the URL and user details will be displayed in the Service Catalog output console page.
To know more about our Cloud adoption practice, click the following link https://www.oneglobesystems.com/cloud-adoption